
cyberstorehut security byte exclusively brings you Mosyle, the only Apple integrated platform. Simply work your Apple device and create an enterprise safe. Our unique integrated approach to management and security combines fully automated hardening and compliance, next-generation EDR, AI-powered Zero Trust, and cutting-edge Apple-specific security solutions for exclusive privilege management with the most powerful and modern Apple MDM on the market. As a result, the fully automated Apple Unified platform, currently trusted by over 45,000 organizations, can make millions of Apple devices function at an affordable cost. Request an extension test Understand why Mosil is everything you need to work with Apple today.
Last weekend, Google found out it was offering malicious websites again at the top of its search as a sponsored result. This is not the first time Google Ads has approved a website that incorporates malware. In fact, the first instance of this dates back to 2007, when the platform (known at the time Google AdWords) promoted fake antivirus software, which was then widely known as “Scullyware.” But in 2025, can Google make this happen with its deep, deep pocket? How do hackers carry that?
This week I would like to briefly discuss this new campaign and how they can pull it out.
Security Byte is a security-centric line every week. cyberstorehut. Each week, we share insights about data privacy, discuss the latest vulnerabilities, and shed light on new threats within Apple’s vast ecosystem of over 2 billion active devices.

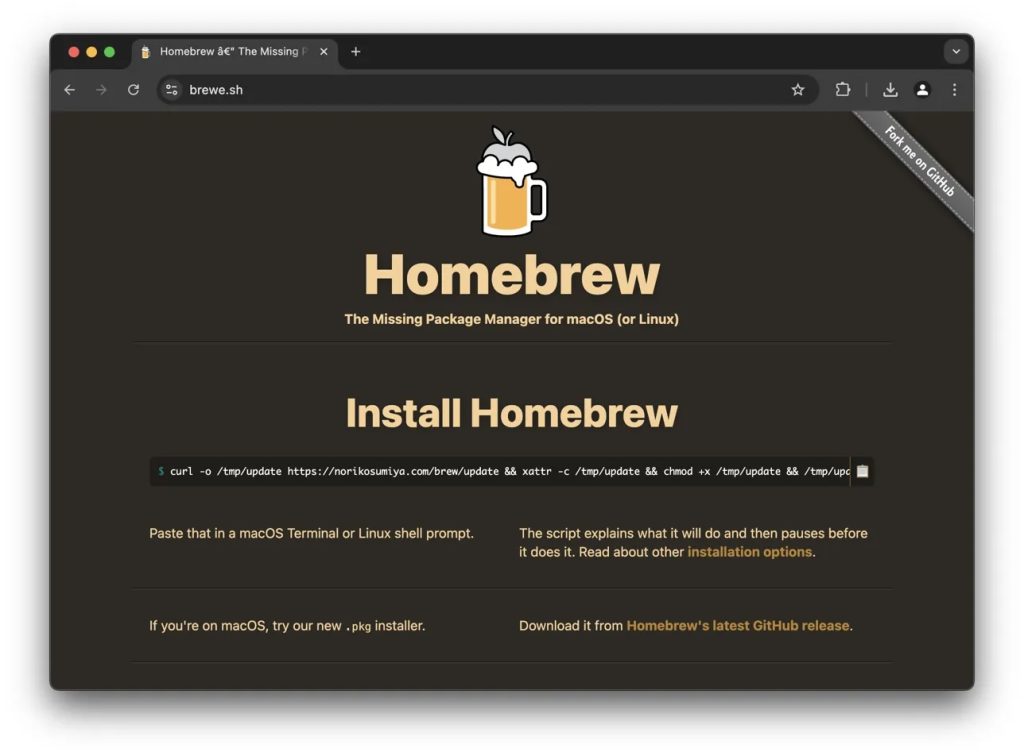
Fake Homebrew ads distribute malware to Mac users
HomeBrew is a widely used open source package manager for MacOS and Linux that allows users to install, update and manage software via the command line.
In a post on X last Saturday, Ryan Chenkie warned other users on the platform that Google is offering ads for malicious clones of popular developer tools, including malware targeting Mac and Linux machines.
Most people can distinguish between fake sites by their URL. Hackers use “0” instead of “O” and “I” instead of “L” and so on. However, in this case, Chenkie found that in Google search, it displays the actual URL of Homebrew (“Brew.sh”) and almost zeroes what’s not a substantial site. However, if you click, the hacker will redirect the potential victim to a malicious clone site (“Brewe.sh”).

On malicious sites, visitors were instructed to install their home brewery by running the command in the terminal. However, unknown to them, when you run this command, it will start downloading and running malware on your Mac or Linux machine.
The malware used in this campaign is called Amos Stealer, also known as “Atomic.” This is an Infostealer explicitly designed for MacOS, with Cybercriminals available as a subscription service of $1,000 per month. Once infected, use the script to start harvesting as much user data as possible. This usually includes iCloud keychain passwords, credit card information, files, and crypto wallet keys stored in your browser. Amos then uses the Curl command to quietly relay the stolen data to the attacker.
Homebrew project leader Mike McQuaid also posted on X to acknowledge the issue, but highlighted the limited capabilities of the project to prevent further occurrence. McQuaid said the cloned site was removed, but simultaneously criticised Google for its insufficient review process, saying, “There’s really little thing you can do about this. It keeps happening again and again. Google seems to like to make money from scammers.
If you’re like me, I’m confused how Google would allow this. In particular, after last year, a fake clone of Google Authenticator, a well-known and trusted, multifactor authentication tool, was approved, showing as a result of pushing the malware to unsuspecting victims.
Techniques used
Like Apple’s App Store review process, Google Ads is not immune to bad actors trying to trick the way they do it as “approved.” Unlike the App Store, however, Google Ads relies heavily on automated systems for reviews, allowing hackers to use clever avoidance techniques.
One common way is to register a domain name that is very similar to a legal name, such as “Brewe.sh” in a recent HomeBrew campaign. From here they can “bait and switch” by first submitting harmless content for approval and later replacing it with a redirect to a malicious site once the ad is approved. Why can’t Google flag it? Hackers can escape this by hijacking Google Ads accounts with clean history and reputation. These often allow you to escape more. Legal URLs will appear in search results until Google crawls again.
Of course, I can’t see how they can do it, but if history had taught us something…
Fortunately, these attacks are usually short-lived due to the Google Ads reporting process. However, even a few hours of exposure can lead to hundreds, if not thousands, of infections. After all, Google search is used by hundreds of millions of people every day.
I trust you, but please check. everytime. ✌✌️
More about Apple Security
- The huge data breaches, including Gravy Analytics, appeared to expose accurate location data to millions of users of popular smartphone apps, including Candy Crush, Tinder, and MyFitnessspal. Here’s what you need to know about deployment violations:
- Washington state is suing T-Mobile for a 2021 security breach that exposed personal data of around 79 million people, including 2m residents of Washington. The data includes Social Security Number, Phone Number, Physical Address, Driver’s License Information, and more.
- A new report from the Checkpoint Survey details how a new variant of the infamous Banshee Steeler malware of Russian-speaking cybercriminals can retrieve pages from Apple’s own security practices to avoid detection
- Subaru security vulnerabilities allowed millions of cars to be remotely tracked, unlocked and started. A full year location history was available and accurate within 5 meters (not necessarily Apple related, but it’s unconventional)
Thank you for reading! Security part-time jobs will be back next Friday.
fOllow Arin: LinkedIn, Thread,
BlueSky


(TagStoTRASSLATE) Google (T) Security Byte







